Image generated by Grok
Since the release of tools like Replit, Claude Code, and Codex, so-called 'vibe coders' have thrown software development into a frenzy. These tools have made it possible for anyone with a computer, an internet connection, and an idea to turn their thoughts into working programs. Imagine a company experiencing a bottleneck in reviewing contracts. A tech-savvy analyst has an idea: 'Let's use Claude to build a lightweight app that summarizes contracts so we can get to the main points and cut down review time.' They put something together in a few hours, and surprisingly, it works. But they have no idea what's actually running under the hood.
What are dependencies?
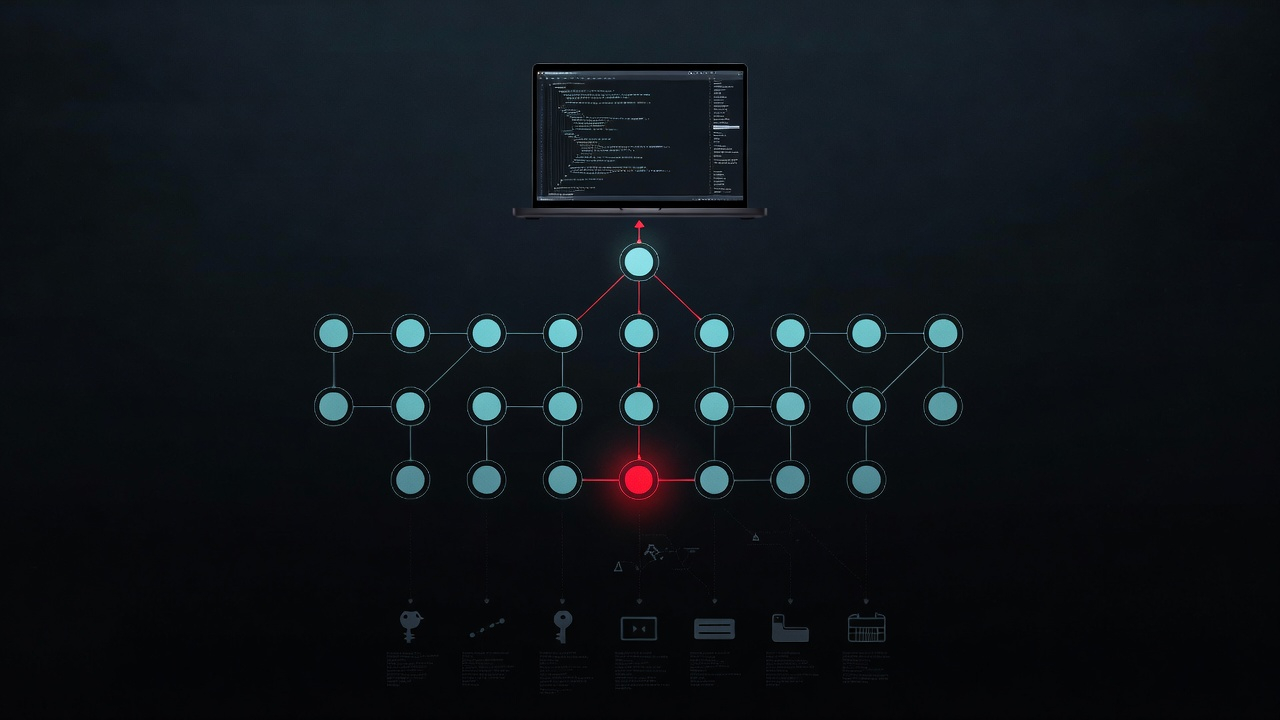
When you build an app, you don't write everything from scratch. Developers use packages, which are pieces of code written by others. These are known as dependencies. These packages are often open source, meaning anyone can use them, even for commercial purposes. As an example, a contract summarizer needs a way for the AI to read the text of a PDF, so the analyst may have installed 'PyPDF', a package that opens PDF files and pulls the text out so the AI can read it. Every time your AI tool is developing software for you, it's pulling these packages into your project. For your software to work, it needs those packages installed. That is why they are called dependencies. This is a widely accepted way to develop software, because many of these packages have been maintained for years and are battle-tested. It also eliminates the need for developers to reinvent the wheel, building on top of what already works. However, there are also risks that most vibe coders aren't aware of. Each package you install has its own dependencies. And those have their own. While you may think you only installed one package, under the hood, there could be a dozen other packages running that you never chose, never saw, and know nothing about. Each one is maintained by someone else, somewhere in the world. If any one of them gets compromised, the analyst's app, and their machine, inherits the problem.
This month, that's exactly what happened.
What happened with LiteLLM
On March 24th, a group called "TeamPCP" published infected versions of "LiteLLM," a package used to route AI requests to different models like Claude or ChatGPT. This package is a dependency to dozens of AI frameworks, is widely deployed across cloud environments, and is downloaded over 3 million times a day. If you used Cursor, Replit, or Claude to build an AI application, your coding tool may have pulled it in automatically without you ever knowing. The infected versions were live for a short window and were downloaded tens of thousands of times.
For those who installed the compromised package, malware ran immediately, putting things like API keys, AWS credentials, and database passwords at risk. To put that in plain terms: your API keys are like credit cards for cloud services. If someone steals your OpenAI or Anthropic key, they can rack up thousands of dollars in charges on your account. Your AWS credentials are the keys to your cloud infrastructure. With those, an attacker can access your databases, read your files, or spin up servers on your dime. Your SSH keys are like a master key to every server you've ever connected to. Losing them is like someone copying every key on your keyring without you knowing. The malware grabbed all of it, packaged it up, encrypted it, and sent it to the attackers. Then it installed a backdoor so it could come back for more. The scary part is this was only found because the malware had a bug and accidentally crashed a developer's machine. Andrej Karpathy, a well-known AI researcher and former head of AI at Tesla, warned that if the attacker had written slightly better code, nobody would have noticed for weeks.
What happened with Telnyx
Three days later, the same group hit Telnyx, a telecom SDK used to build AI voice agents. In plain terms, an SDK (Software Development Kit) is a pre-built toolkit that connects your app to someone else's service. Going back to the contract analyzer, the analyst likely installed the OpenAI SDK so their application could talk to ChatGPT. For a developer working on a customer service tool, they might install the Telnyx SDK so their app could make and receive phone calls. In this attack, the malware was hidden inside an audio file and was designed to evade common security tools like network scanners and firewalls. The malware remained invisible until it ran. This attack targeted multiple operating systems, including Windows, where it dropped a file disguised as a legitimate Microsoft tool that ran silently every time you logged in. The first malicious version contained a coding error that broke the payload, which the attackers fixed in a second version published shortly after.
How they got in
TeamPCP didn't hack these packages directly. Ironically, they compromised Trivy, a security vulnerability scanner. When LiteLLM ran Trivy as part of its security checks, the poisoned scanner stole the credentials used to publish the package. Those credentials were then used to push the malicious versions. In short, a security tool meant to protect you became the weapon.
How it all connects
The Telnyx credentials may have been stolen from a developer or build system that had the compromised version of LiteLLM installed. Each attack feeds the next. Every victim essentially hands the attackers the keys to their next target.
The full timeline this month
- March 19: Trivy (security scanner) compromised
- March 20: Dozens of npm packages hit via stolen tokens
- March 23: Checkmarx KICS (infrastructure scanning tool) compromised
- March 24: LiteLLM poisoned on PyPI
- March 27: Telnyx poisoned on PyPI
Five attacks in eight days. And they've reportedly partnered with a ransomware group to monetize what they've stolen.
And it's not just one group
While TeamPCP was running their campaign, a completely separate attacker hit Axios on March 31st. Axios is a JavaScript library used to make web requests. Remember the OpenAI SDK the analyst installed so their app could talk to ChatGPT? Axios is one of the packages running underneath it. The analyst never installed it, never saw it, and probably doesn't know it's there. Axios is one of the most widely used packages in the JavaScript ecosystem, with over 100 million downloads weekly. If your app talks to an API, there's a good chance Axios is somewhere in your dependency tree. In this instance, the attacker hijacked the account of the developer who manages Axios, changed their credentials, and pushed two malicious versions of the package, which were live for about three hours.
What makes this attack particularly dangerous is that the malware erased its own tracks after running. It deleted the malicious code, replaced it with a clean-looking file, and exited silently. If you check your project now, everything looks normal, even if you were hit. The only reliable sign is the presence of a package called plain-crypto-js in your node_modules folder, a package that has never appeared in any legitimate version of Axios.
An automated security scanner caught it within minutes of publication. But it still took nearly three hours to pull the compromised versions down. That gap is the problem.
My experience with this
For nearly two years I've been building AI tools and infrastructure, and have used tools like Claude Code to develop things I never thought I would be able to. For the first few months this was exhilarating. I could create anything my mind thought of within an hour and have it running in the next. However, as time went on I learned the limitations and risks that most people building with AI tools may not be prepared for. When the news broke about LiteLLM, that hit home. I checked every environment on my machines and thankfully none of the compromised packages were installed. But the fact that I had to manually check, Googling commands and cross-referencing version numbers at midnight, told me something was broken. I knew dependency security was a gap, not just for me, but for anyone building with these tools. I couldn't find anything that was straightforward enough for someone outside the DevOps world. And while there are tools like Snyk, Dependabot, and Trivy (the same software that was compromised), they didn't fit what I was looking for. So I built one.
What I built
KORSCAN is a dependency vulnerability scanner for builders who want a simple way to see if they are exposed to known vulnerabilities. You set up a project through a guided wizard that asks what operating system you're on, what language you use, and it gives you the exact commands to run on your machine. You paste that output into the scanner, which checks your packages against several public security databases. When something is found, it explains what's wrong and how to fix it in plain English. KORSCAN never connects to your machine or your codebase. You paste the output in. That's it. There's no access to your source code, no credentials stored, no background agent running. After what happened with Trivy, that distinction matters. Once your project is set up, KORSCAN is designed to track your dependencies and check security databases daily. If something in your project gets compromised in the future, you should receive an email alert with the problem and the solution. The only friction is that as you add or update packages in your project, you'll need to update your scan. But that's the trade-off for knowing your dependencies are checked. I built this for myself but realized many like me need something similar.
To be clear, a tool like KORSCAN is a starting point, not a replacement for professional security expertise. If you're building anything that handles sensitive data, working with a cybersecurity professional should be part of your plan. KORSCAN helps you see the problem. A cybersecurity professional helps you figure out what to do about it.
A note on the term vibe coder. The label gets thrown around loosely, and some of it is earned. There are people shipping reckless code with no understanding of what they've built. But there are also people who are thoughtful, who know their limits, and who take the time to learn while working toward a real vision. If you're someone who is thoughtful, knows their limits, and takes the time to learn, this was written with you in mind. Follow me for more on building responsibly with AI.
The numbers
These are real numbers.
- LiteLLM: 97 million downloads per month. Widely deployed across cloud environments.
- Axios: over 100 million weekly downloads. One of the most widely used packages in the JavaScript ecosystem.
- Telnyx: hundreds of thousands of downloads per month. Used by enterprise contact centers and AI voice platforms.
- CISA added the underlying vulnerability to its Known Exploited Vulnerabilities catalog, with a federal remediation deadline in April 2026.
- TeamPCP has reportedly partnered with the Vect ransomware group to monetize stolen credentials through a large affiliate network.
- The average supply chain breach costs millions. For U.S. organizations, that number is even higher.
What you should do right now
Check if you have litellm or telnyx installed:
pip show litellm
pip show telnyxNote: these commands show what's currently installed. If you've already updated to a newer version, your machine may still be compromised from a previous install. When in doubt, rotate your credentials anyway.
If litellm shows version 1.82.7 or 1.82.8, or telnyx shows 4.87.1 or 4.87.2, treat that machine as compromised. Rotate every credential that was accessible to that environment. Every API key. Every cloud token. Every SSH key. Not just the ones you think were exposed, all of them.
For Axios, check your node_modules folder for a package called plain-crypto-js. If it's there, treat that machine as compromised and follow the same steps.
If you build software and you've never scanned your dependencies, start now. It takes five minutes to check. If you don't, everything on your machine is at risk.
One scan, no credit card. If you want ongoing monitoring and daily alerts, Pro is $9.99/month during beta.
Sources
- LiteLLM Official Security Update — docs.litellm.ai
- Snyk: "How a Poisoned Security Scanner Became the Key to Backdooring LiteLLM" — snyk.io
- Endor Labs: "TeamPCP Strikes Again: Telnyx Compromised Three Days After LiteLLM" — endorlabs.com
- Telnyx Security Notice — telnyx.com
- Wiz: "Three's a Crowd: TeamPCP Trojanizes LiteLLM" — wiz.io
- Arctic Wolf: TeamPCP Supply Chain Attack Campaign Advisory — arcticwolf.com
- Socket.dev: Multi-stage Attack Chain Analysis — socket.dev
- Socket.dev: Axios Supply Chain Compromise Analysis — socket.dev
- StepSecurity: Axios npm Account Hijack Technical Analysis — stepsecurity.io
- CISA Known Exploited Vulnerabilities Catalog: CVE-2026-33634 — cisa.gov
- GitHub Advisory: GHSA-fw8c-xr5c-95f9 — github.com